
AI Chatbot Penetration Testing Methodology: A Technical Deep Dive
A technical deep dive into AI chatbot penetration testing methodology: how professional security teams approach LLM assessments, what each phase covers, and wha...
Browse all content in the Technology and Development category

A technical deep dive into AI chatbot penetration testing methodology: how professional security teams approach LLM assessments, what each phase covers, and wha...

Google's Gemma 4 shipped without Multi-Token Prediction heads, despite being trained with them. We explain what MTP is, why it matters for inference speed, and ...

We fine-tuned Google's Gemma 4 31B model on a MacBook Pro M3 Max to generate sports articles. Here's how it compared to Claude Sonnet in quality, speed, and cos...

The OWASP GenAI Security Project defines a five-category minimum bar for secure MCP server deployment. Use this checklist to assess your current posture across ...
Prompt injection is the primary attack vector against MCP servers in production. Learn the four OWASP-recommended controls: structured tool invocation, Human-in...

Authentication is the most critical security layer for remote MCP servers. Learn why OAuth 2.1 with OIDC is mandatory, how token delegation prevents the Confuse...

Tool poisoning and rug pulls are two of the most dangerous MCP-specific attack vectors. Learn how attackers embed malicious instructions in tool descriptions an...
AI red teaming and traditional penetration testing address different aspects of AI security. This guide explains the key differences, when to use each approach,...
AI chatbots with access to sensitive data are prime data exfiltration targets. Learn how attackers extract PII, credentials, and business intelligence through p...

Jailbreaking AI chatbots bypasses safety guardrails to make the model behave outside its intended boundaries. Learn the most common techniques — DAN, role-play,...

LLM APIs face unique abuse scenarios beyond traditional API security. Learn how to secure LLM API deployments against authentication abuse, rate limit bypass, p...
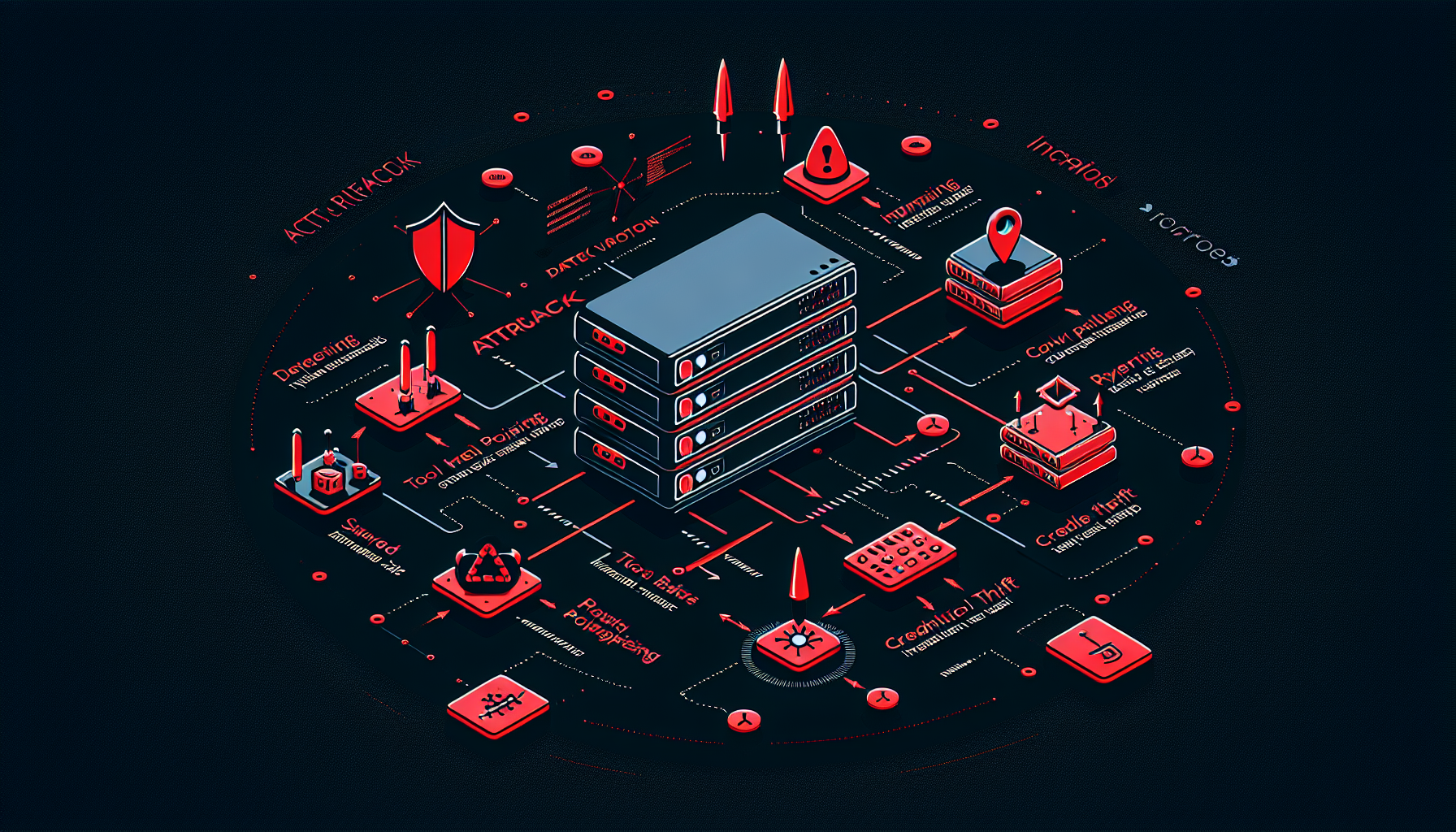
MCP servers expose a unique attack surface combining traditional API risks with AI-specific threats. Learn the 6 critical vulnerabilities identified by OWASP Ge...

The complete technical guide to OWASP LLM Top 10 — covering all 10 vulnerability categories with real attack examples, severity context, and concrete remediatio...

Prompt injection is the #1 LLM security risk. Learn how attackers hijack AI chatbots through direct and indirect injection, with real-world examples and concret...

RAG poisoning attacks contaminate the knowledge base of retrieval-augmented AI systems, causing chatbots to serve attacker-controlled content to users. Learn ho...

Autonomous AI agents face unique security challenges beyond chatbots. When AI can browse the web, execute code, send emails, and call APIs, the blast radius of ...
Discover Rendervid, the free open-source alternative to Remotion for programmatic video generation. AI-first design with MCP integration, JSON templates, cloud ...

Explore a sophisticated CrewAI workflow that automates SEO article generation, from topic ideation and keyword research to content creation and publishing, all ...

FlowHunt releases an open-source CLI toolkit for evaluating AI flows with advanced reporting capabilities. Learn how we implemented LLM as a Judge using our own...

Explore the top large language models (LLMs) for coding in June 2025. This complete educational guide provides insights, comparisons, and practical tips for stu...

A technical founder's guide to implementing AI commerce protocols (UCP, ACP, AP2), mastering technical SEO fundamentals, and generating content optimized for bo...
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.